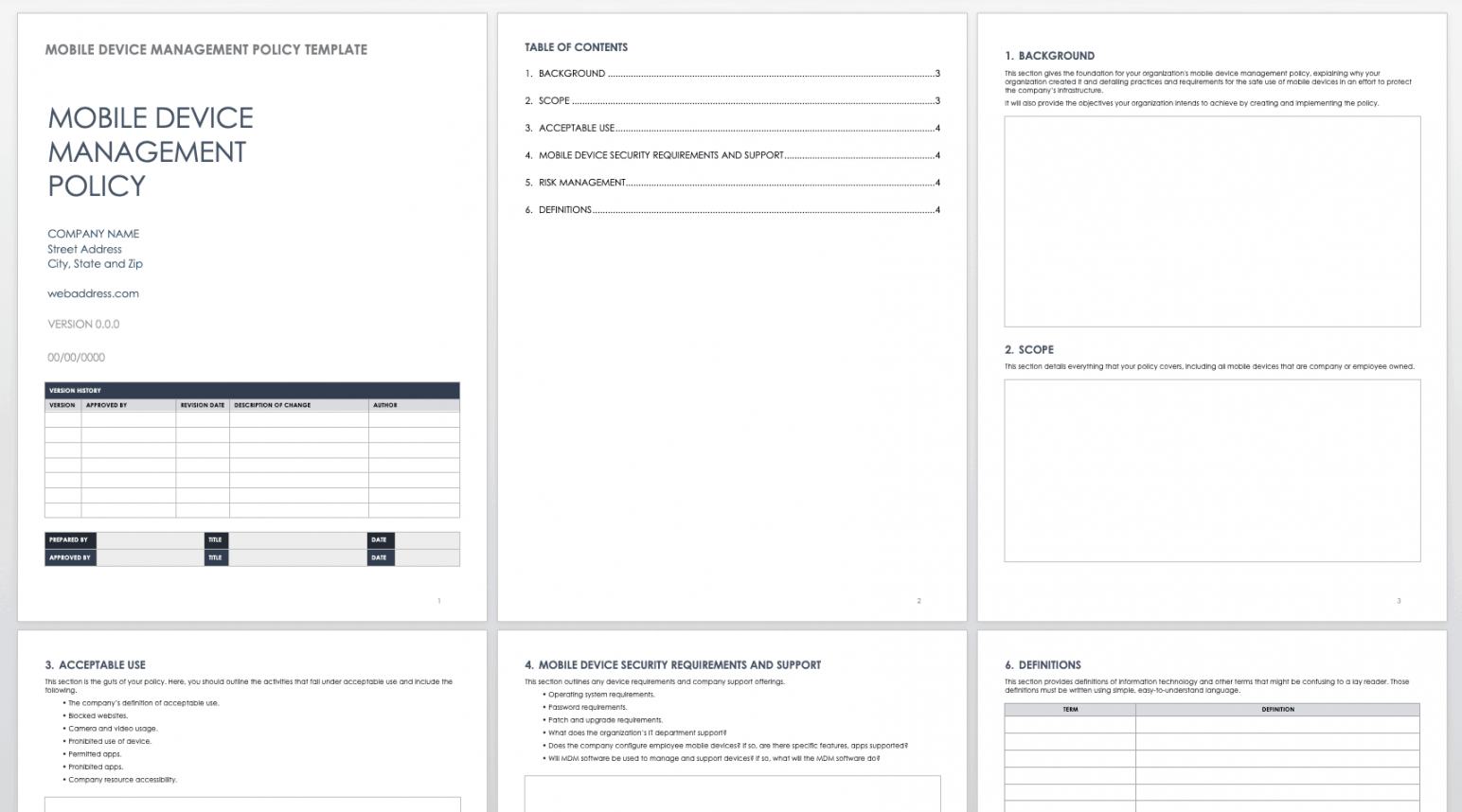
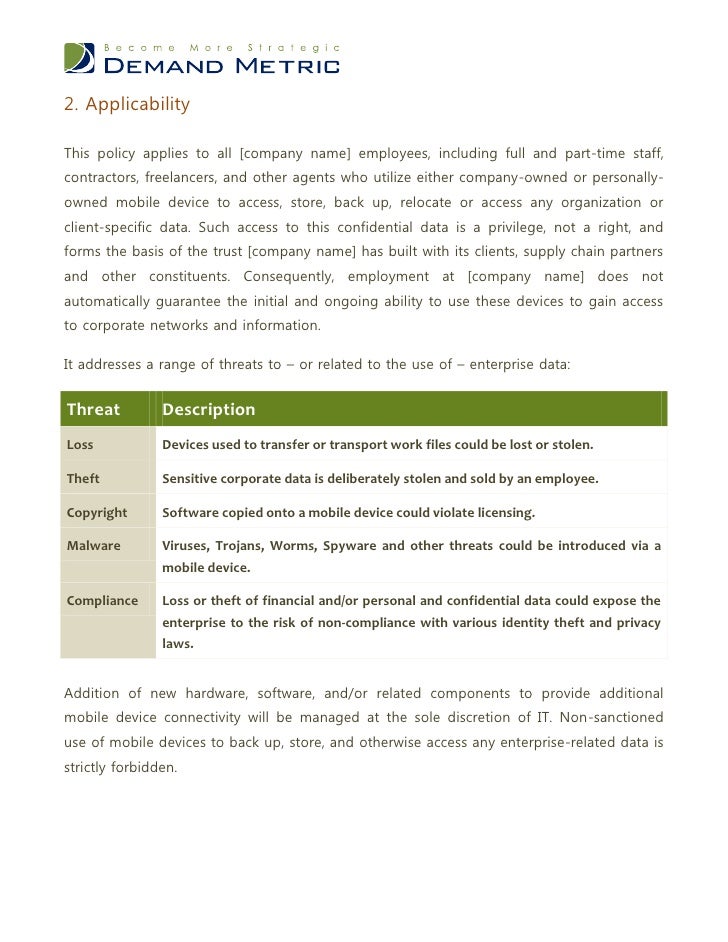
Mobile Device Acceptable Use Policy Template. This policy applies to all workers, including full and part-time staff, contractors, freelancers, and different agents who use any cell gadget to entry, retailer, backup, or relocate any organization or client-specific knowledge. Using a tool safety supervisor can help enforce these measures and stop eventualities that would compromise gadgets. Our templates and insurance policies are designed by Lead Auditors certified in ISO 27001. Wikipedia receives between 25,000 and 60,000-page requests per second, depending on the time of the day.
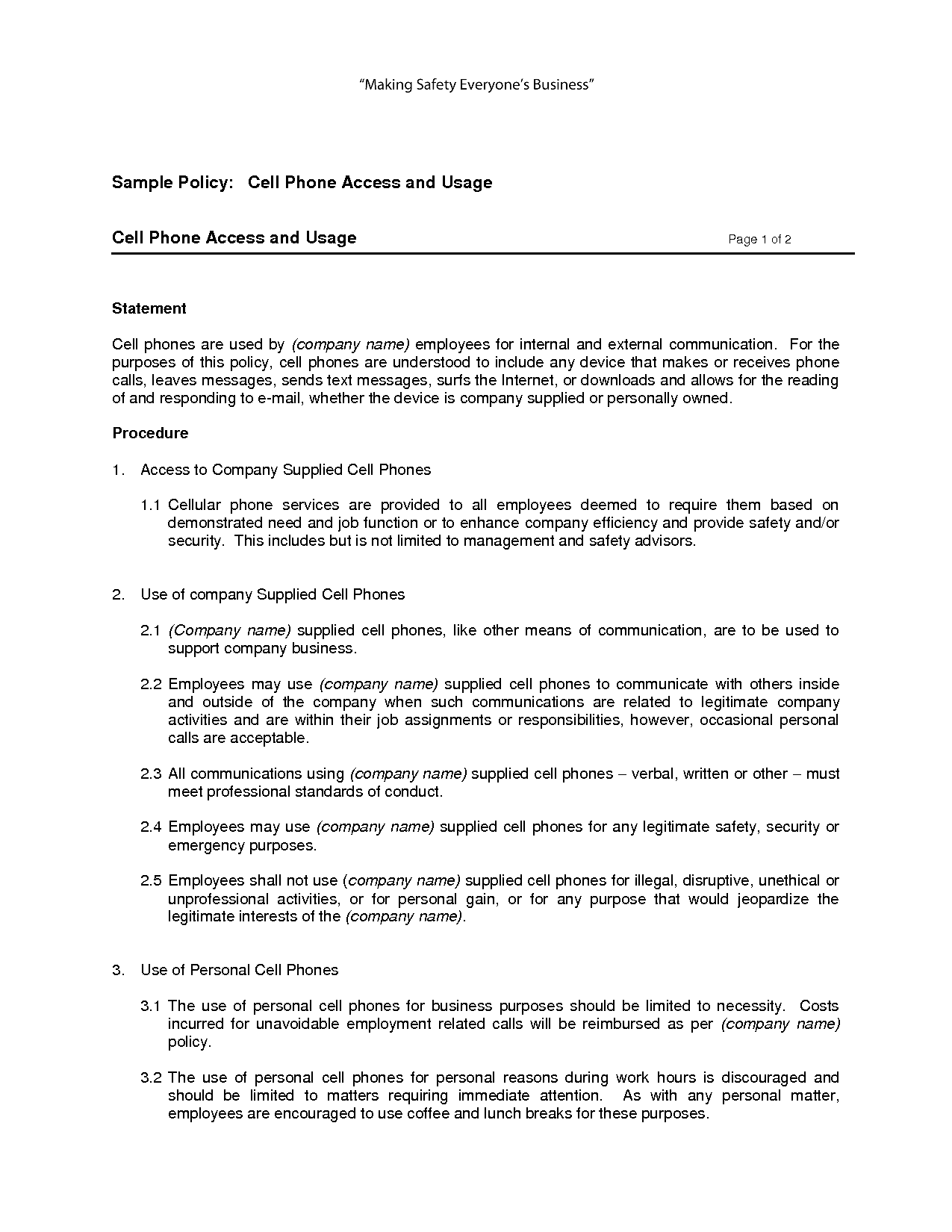
Transfer of numbers and gear might be made on a case by case basis by every department. The waiver only applies to gadgets which are utilized to entry assets. Connectivity of all cell units shall be centrally managed by ’s IT division and can use authentication and powerful encryption measures.
Many multi-factor authentication products require customers to deploy shopper software program to make multi-factor authentication methods work. The IT Director, with enter from the leadership inside the College or Division, will decide device assignments offering users choices where possible. Personnel touring to a High-Risk location, as outlined by FBI and Office of Foreign Asset control, should contact IT for approval to journey with corporate property. A third-party authenticator app allows two-factor authentication, normally by displaying a randomly generated and regularly altering code to use for authentication. Employees who separate from employment with outstanding equipment money owed or incur unauthorized expenses will be thought-about to have left employment on unsatisfactory phrases and could also be subject to authorized motion for recovery of the loss.
As of 2021, web page requests are first handed to a front-end layer of Varnish caching servers and back-end layer caching is done by Apache Traffic Server. Further statistics, primarily based on a publicly available 3-month Wikipedia access hint, can be found.

Physical tokens often don’t scale, usually requiring a brand new token for each new account and system. Procuring and subsequently changing tokens of this kind includes prices.
Mobile Gadget Remote Wipe Waiver
Such trails will be in a position to monitor the attachment of an external system to the corporate network, and the ensuing stories may be used for investigation of attainable breaches and/or misuse. The end person agrees to and accepts that his or her entry and/or connection to ’s networks could additionally be monitored to report dates, instances, duration of access, and so on. in order to determine uncommon usage patterns or other suspicious exercise. The standing of the device, including location, IP handle, Serial Number, IMEI, may be monitored.
In addition to the usual malware risks that would occur if you connect a portable storage system to a computer, there are several proof-of-concept malicious USB units that have been created by cybersecurity researchers. If the gadget is not wanted for University enterprise, it’s to be returned to the related College or Division’s IT Director. Mobile Devices deemed Excess Property are re-sold through the University’s established Excess Property disposal procedures and techniques.
Firm
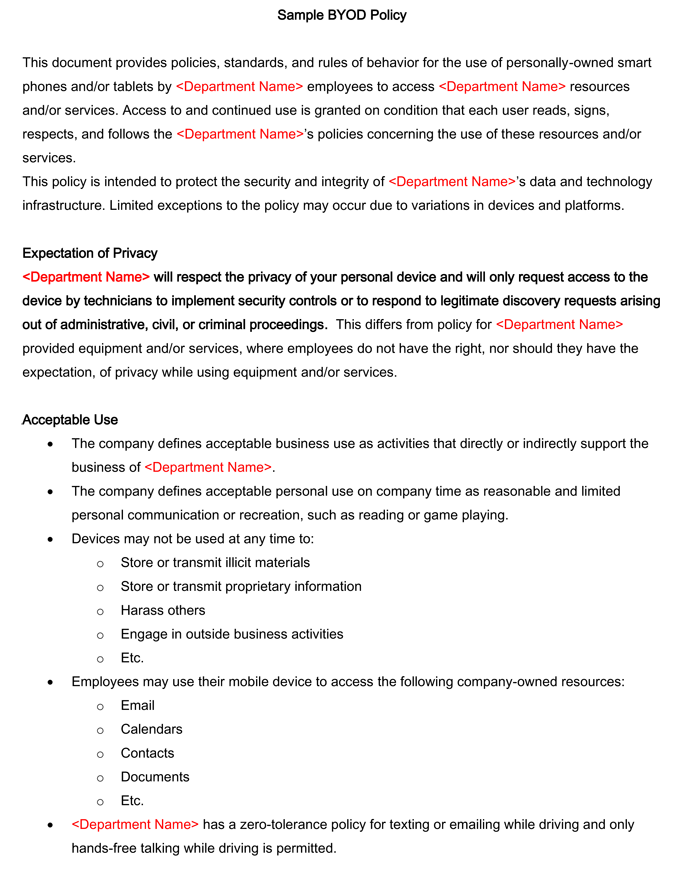
Users are imagined to rely solely on corporate-approved suppliers whereas dealing with delicate work information. Backing up of work and private data falls underneath the accountability of the users.

Detailed usage stories can be found to any supervisor upon request by contacting Telecommunications. Passwords and different confidential knowledge, as defined by ’s IT department, are to not be saved unencrypted on mobile units. Prior to initial use on the corporate network or associated infrastructure, all cell units have to be permitted by IT.
Plan For A Way You’ll Use Activity Monitoring Data
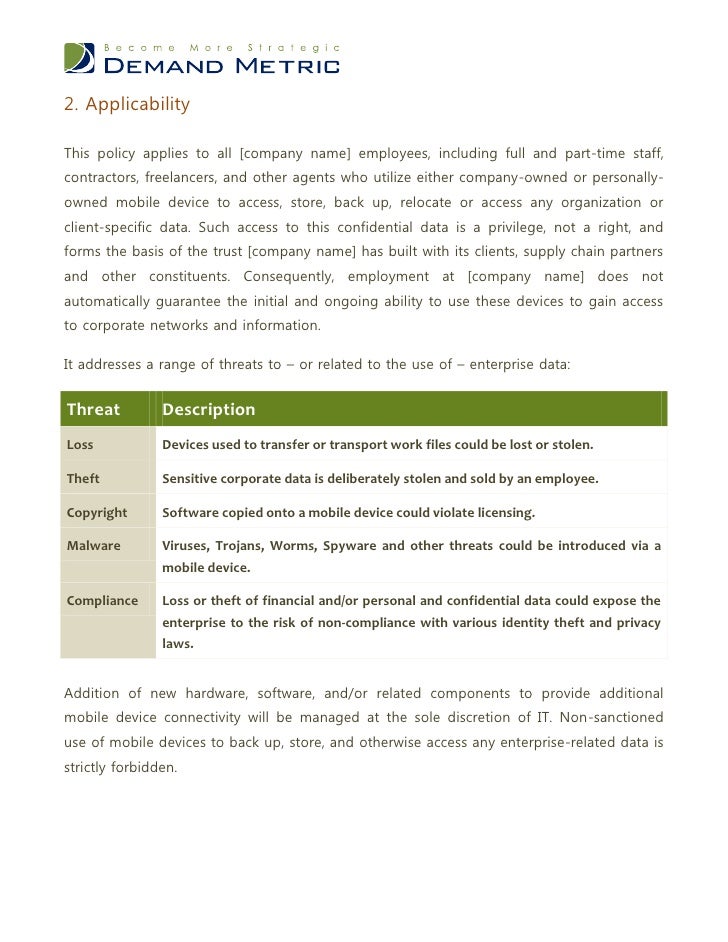
Consequently, employment at does not automatically guarantee the initial or ongoing ability to make use of these gadgets to achieve access to company networks and information. In response to the publication, numerous authentication distributors began improperly promoting challenge-questions, secret photographs, and other knowledge-based strategies as “multi-factor” authentication. While templates can function a construction for understanding the core ideas, you cannot afford to forgo mindfully contemplating the elements which may be essential in your company’s information safety needs.
It is important to notice that while average and high-risk assets should be prioritized, even low-risk endpoints must meet minimal security standards to stop them from becoming a vulnerability as a result of mismanagement. The policies you develop will be closely influenced by the belongings that you just handle. Each gadget has a novel threat level and accompanying administration needs.
Personnel found to have violated this coverage may be topic to disciplinary action, as a lot as and including termination of employment, and related civil or criminal penalties. All information situated on Information Resources are owned by may be topic to open information requests and could additionally be accessed in accordance with this policy.
Plan For A Way You’ll Use Exercise Monitoring Information
Vendors similar to Uber have mandated by the bank to amend their payment processing systems in compliance with this two-factor authentication rollout. No further tokens are necessary as a end result of it makes use of cell units which are carried on a daily basis.
If your preferred system does not seem on this list, contact the helpdesk at [e-mail address] or . Although IT at present only allows listed devices to be related to enterprise infrastructure, it reserves the right to update this listing in the future.
Don’t Reinvent And Create Iso 27001 Insurance Policies From Scratch!
She uses endpoint exercise monitoring to make sure that system activity may be traced to a particular consumer in the event that an information breach is found. Only company-provided encrypted USB devices are allowed to be used for transmitting information.
Some Services and Software could present choices that let you Share your Content with different clients or to make it public. “Share” means to e mail, post, transmit, stream, addContent, or in any other case make available by means of your use of the Services and Software.
The major downside of authentication including something the user possesses is that the consumer should carry around the bodily token , practically always. Many organizations forbid carrying USB and electronic devices in or out of premises owing to malware and knowledge theft risks, and most essential machines do not have USB ports for a similar reason.
The DriveStrike group recommends implementing and implementing mobile gadget management finest practices and insurance policies. Companies with workers, contractors, or distributors who access firm knowledge using any cell computing device are sensible to proactively implement data breach protection measures together with however not restricted to distant wipe. Using a device safety supervisor can help enforce these measures and forestall situations that might compromise devices.

Any attempts to bypass USB permissions will ship alerts to his safety personnel for immediate investigation. A laptop that is used for sheep dipping will not be connected to the internet or the local area community; this helps stop attackers from infiltrating the community via the sheep-dip computer and prevents the unfold of laptop worms.
She needs to use USB activity monitoring to alert her to incidents of her workers trying to carry out illicit data transfers. Reports on all file operations & devices related to endpoints are reviewed by Sam each day.

DriveStrike is right here that can assist you defend your most critical information with premium quality endpoint security. Start a free trial with DriveStrike today, and get in contact with us when you need any assistance. The insights from these reports can be used to determine non-compliant customers utilizing endpoint gadgets in an insecure method, gather proof of illicit file transfer attempts, and monitor the peripheral units used within your organization.
For a low month-to-month value, entry and acquire unbelievable digital property, like fonts, inventory pictures, and way more. That means so long as you’ve received got your subscription obtain as a lot as you want from the massive Envato Elements premium content material material library with no caps.

Attempts to use private USB gadgets are blocked by her endpoint safety software program and an e mail alert is shipped to her safety staff for evaluation. All departments should keep accurate and up-to-date information of the removable media devices issued within the group.
In May 2017 O2 Telefónica, a German cell service supplier, confirmed that cybercriminals had exploited SS7 vulnerabilities to bypass SMS based mostly two-step authentication to do unauthorized withdrawals from customers financial institution accounts. The criminals first contaminated the account holder’s computers in an attempt to steal their checking account credentials and cellphone numbers. Then the attackers bought access to a fake telecom provider and set up a redirect for the victim’s telephone number to a handset controlled by them.
This sort of token principally makes use of a OTP that may solely be used for that particular session. Our toolkit accommodates 27 ready to use and editable ISO policies and procedures.
Determine the members that may tackle the position of Information Security Officer or an identical place. Your designated safety personnel will be answerable for guaranteeing that policies are reviewed appropriately, together with the opposite key obligations as outlined by your organization’s distinctive regulatory requirements.
Applications that aren’t accredited by IT usually are not to be used within the office or along side company data. Usage of a mobile system to seize photographs, video, or audio, whether native to the gadget or through third-party purposes, is prohibited inside the workplace. Notwithstanding the popularity of SMS verification, safety advocates have publicly criticized SMS verification and in July 2016 a United States NIST draft guideline proposed deprecating it as a type of authentication.

When sensitive data is saved on removable media, the system have to be encrypted and password-protected to prevent unauthorized disclosure of the information. The password should be distinctive, troublesome to guess, and not shared with some other parties. The safe use of removable media devices is just one aspect of a complete data security program that must be adopted to successfully safeguard delicate info.

Apple shifted its consideration to premium smartphones in the newest iPhone 14 lineup with features corresponding to Lockdown Mode that IT … The HIPAA Security Officer, Chief Operating Officer, and quick manager or director shall be advised of breaches of this coverage and might be liable for applicable remedial motion. The go-to useful resource for IT professionals from all corners of the tech world looking for innovative expertise options that clear up their unique enterprise challenges.
Devices that are not approved by IT, usually are not in compliance with IT’s safety policies, or symbolize any menace to the company community or data is not going to be allowed to connect. Devices might only entry the company network and knowledge via the Internet utilizing a Secure Socket Layer Virtual Private Network connection.
- Passwords and different confidential data, as outlined by ’s IT department, are not to be saved unencrypted on cellular devices.
- The end user agrees to right away report back to his/her manager and ’s IT department any incident or suspected incidents of unauthorized knowledge entry, information loss, and/or disclosure of firm sources, databases, networks, and so forth.
- Auto-forwarding electronic messages outside the interior systems is prohibited.
- Dale’s diverse multimedia background permits him the opportunity to produce a wide selection of content for CurrentWare including blogs, infographics, videos, eBooks, and social media shareables.
A information loss occasion sometimes happens because of intentional or unintentional deletion, a malicious assault that leads to data corruption, or bodily harm to knowledge storage hardware. Collecting end-user feedback in your endpoint security and administration framework provides you with the perfect alternative to determine parts of your coverage that will trigger an sudden productivity bottleneck.
Once any software leaves the confines of your office, the risk of security breaches places your gear and sensitive information at risk. On a cell system, the Acceptable Use Policy can open when somebody downloads or opens your app for the first time.

This also permits a consumer to move between workplaces and dynamically obtain the identical stage of community access in each. While John’s precise position is prime secret, we do know that he works in the area of Military Intelligence.

This should be completed by the particular person, then verified by the College’s or Division’s IT Director previous to when the model new system is assigned. Excess Property will preserve a list of all University owned cell models obtainable for either repurposing, recycling, or reuse. For a low monthly worth, entry and obtain unbelievable digital property, like fonts, inventory pictures, and far more.
Smart cell devices corresponding to smartphones, tablets, and laptops will access the corporate community and information using cellular VPN software program put in on the system by IT. These policies function a important administrative safety management for managing the dangers of moveable storage units.