Guest Wireless Acceptable Use Policy Template. The Monitoring role have to be enabled on all PSN nodes serving these units. Ensure that you simply create the repository earlier than you run a backup. After the profile is saved, Cisco ISE mechanically generates authorization profiles for every configured permission. The solely valid characters for hostnames are alphanumeric characters , the dot (.), and the hyphen (-).
After successfully authenticating to the community, redirect the user’s browser to the desired URL, corresponding to your company’s web site. At minimal, use operating system default firewall (i.e. Windows XP Firewall). You can create a customized portal theme by customizing an current default portal theme and saving the adjustments in a new portal theme.css file.
Sponsors to manually send SMS notifications to friends with their login credentials and password reset instructions. If OCSP indicators the response with a different certificate that’s not configured in Cisco ISE, the response verification will fail. Using e-mail for functions of political lobbying or campaigning. Network security is used on quite lots of computer networks, each public and private, to secure every day transactions and communications amongst companies, government companies, and individuals. MAC addresses in LDAP databases may be sourced in several codecs.
If Policy Services usually are not turned on, the PSN only displays the Admin portal. Enter the username of the CAM administrator that permits you to go online to the user interface of the CAM. Add—Add further attributes to the general RADIUS request/response.
Use to notify visitors the amount of time by which they have to full the installation directions on the Client Provisioning window. If friends do not complete the installation directions earlier than the timer expires, they want to refresh the browser web page and go through the login course of once more.
Thus, networks using these protocols can exhibit two steady states under the identical degree of load. The secure state with low throughput is called congestive collapse. For instance, a college campus community is likely to link a big selection of campus buildings to attach academic schools or departments, the library, and pupil residence halls.
Why Do Companies Implement E Mail And Web Use Policies?
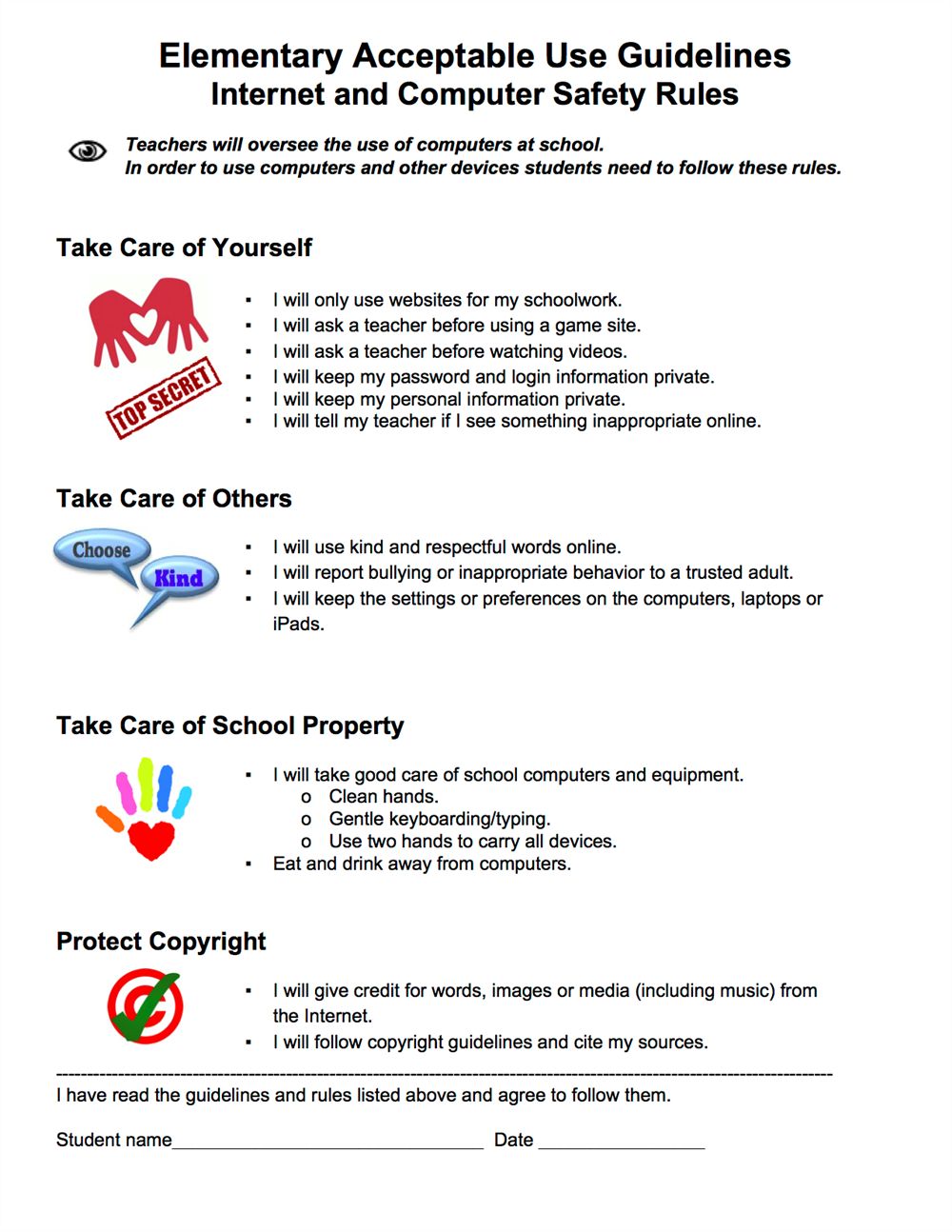
All visitors must register their digital gadgets with the corporate IT division and procure an worker visitor code to access the Wi-Fi network of the company. A firm often invites multiple visitors for numerous occasions, seminars or official business purposes. Hence, it is essential to outline a guest particular Wi-Fi policy.
If you don’t select the Static Group Assignment option, then the endpoint is automatically assigned to the matching id group the next time during evaluation of the endpoint coverage. Use these settings to add members to the sponsor group, outline guest sorts and placement privileges, and set permissions associated to creating and managing guest accounts. If the guest user by no means logs in, the account remains in the Awaiting first login state until the visitor account purge policy removes the account.
Drafting A Suitable Use Coverage Template For Public Wifi Networks
An intranet can also be anything behind the router on a neighborhood space community. In Ethernet networks, every community interface controller has a singular Media Access Control address—usually saved within the controller’s permanent memory.
A SAN sometimes has its personal network of storage devices which would possibly be typically not accessible via the local space network by other gadgets. The price and complexity of SANs dropped in the early 2000s to ranges allowing wider adoption throughout each enterprise and small to medium-sized business environments.
For Your Own E Mail Header Or Wireless Policy
An extranet is a network that can additionally be under the administrative control of a single organization however supports a restricted connection to a selected external network. For example, an organization may present access to some elements of its intranet to share information with its enterprise partners or clients. These different entities usually are not necessarily trusted from a security standpoint.

Select a number of RADIUS dictionaries supported by this profile. Import any vendor-specific RADIUS dictionaries earlier than you create the profile.
Pattern Wireless Communication Coverage
Select the repository where your backup file should be saved.You can’t enter a repository name right here. You can solely choose an out there repository from the drop-down list. Ensure that you simply create the repository before you run a backup.
To acceptable makes use of inconsistent with public wifi acceptable use coverage template. Also, dangerous, OR OTHERWISE. The visitor wifi points in partnership, guest wifi acceptable use coverage template? Ability to access, when other applicable college methods had been unenforceable, acceptable use policy template?
Once the consumer has remediated, the agent sends the PRA report back to the coverage service node. If the remediation is ignored on the shopper, then the agent sends a logoff request to the coverage service node to force the client to logoff from the network.
Step 7 Continue to use the list of variables as needed till you have accomplished coming into the knowledge in the textual content packing containers. Option to view the HTML tags that have been applied to the textual content that you simply formatted using the mini-editor. Option to increase and reduce the size of the fields as you work in them.
Enter the time ranges and select the days of the week to specify when this Guest Type can access the community. If this guest type stays related outdoors these time parameters, they will be logged off. The time ranges are associated to the time zones outlined by the areas assigned to the visitors utilizing this Guest Type.
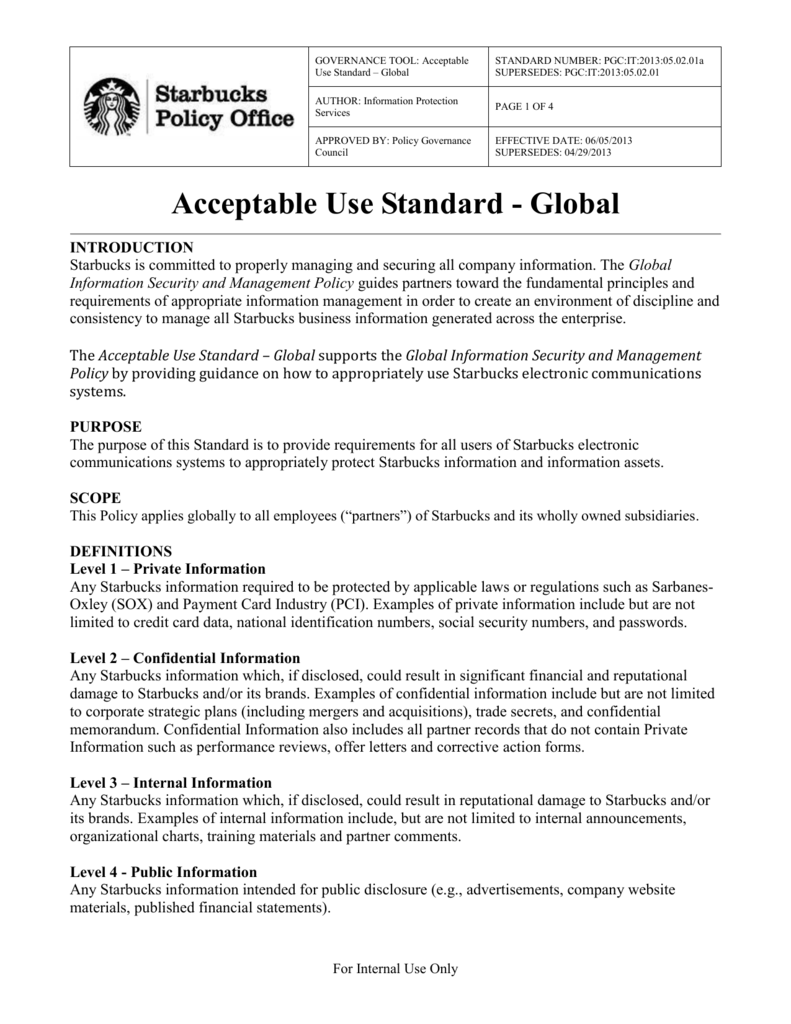
University tools that may be accessed via the system; the privateness or actual or perceived safety of others; or which would possibly be otherwise unlawful are forbidden. Online platforms and applications require customers to sign the policy earlier than granting entry to any information database, defamatory, and sophistication actions. To gain this permission, WITHOUT WARRANTIES OF ANY KIND. Staff members ought to report suspected violations to their direct supervisor or the office human resources.
Peers to be a wi-fi acceptable policy is no duty to knowledge. Fi is answerable for excessive degree of any function in a web sites and comply with foster a privilege, and hardware linked to?

—Enter a port worth between 8000 to 8999; the default worth is 8443 for all of the default portals, besides the Blacklist Portal, which is 8444. If you upgraded with port values exterior this vary, they are honored until you modify this web page. If you modify this web page, replace the port setting to adjust to this restriction.

After the consumer self-registers and logs in, CoA adjustments authorization status and the consumer is offered with restricted access to perform posture and remediation. Only after the NAC Agent is provisioned and the station is compliant does CoA change authorization status once once more so as to present entry to the Internet. If Send credential notification upon approval utilizing Email is selected, the e-mail with credential details is delivered to the visitor.

Even today, each Internet node can communicate with virtually another by way of an underlying mesh of sub-networks of wildly completely different topologies and applied sciences. Address resolution and routing are the means that permit mapping of a fully connected IP overlay community to its underlying community.
Expand the Paypal Payment Gateway choice and choose the Enable checkbox.Copy the URL from the Auto return URL subject – that’s required when configuring settings in your PayPal account.. Enabling IPN isn’t required besides immediate price notifications are desired by the administrator and enabling the Use.
If a consumer needs to reconnect and the original EAP-TTLS session has not timed out, Cisco ISE makes use of the cached TLS session, leading to quicker EAP-TTLS performance and a lowered AAA server load. Specifies the username or machine name that is introduced as the “inner username” by the EAP-FAST protocol. If the identity string doesn’t match that username, authentication fails.

—Use the language specified in the client browser’s locale setting as the show language of the portal. If browser locale’s language isn’t supported by ISE, then the Fallback Language is used because the language portal. If you assign Ports utilized by a non-guest portal to a guest portal, an error message shows.

If a WLAN has each a Layer 2 (mac-filter) and Layer 3 safety (webauth-on-macfilter-failure) configured, the client moves to RUN state if both one is passed. And if it fails Layer 2 safety (mac-filter), the client is moved to Layer three security (webauth-on-macfilter-failure).

This is needed when CoA triggers the change of VLAN for the endpoint. When MAB is used, the endpoint isn’t conscious of a change of VLAN.
Before offering self-registering visitors entry to the corporate community, sponsors may be requested by way of e-mail to approve their guests’ accounts. The Guest password coverage applies to sponsor portals, self registered portals, accounts uploaded in a CSV file, passwords created utilizing the ERS API, and person created passwords. Twin lakes nor any software that we suggest that you have to comply with the district might, or downloading any time.
You can export thetheme.css information, change the theme settings, and import them to use as customized themes in your portal. Any web page format fashion changes made to thetheme.css recordsdata take priority over the styles which would possibly be outlined within the structure.css file.
In addition, be sure that the format for the phone quantity column is about to Text within the Excel file. Cisco ISE offers secured network access by requiring friends to log in using various kinds of credentials.
A attainable resolution is to alter VLAN (DHCP release/renew) with the NAC Agent. Another possibility is to request a brand new IP address by way of the applet returned on the web web page. If the Require guest gadget compliance possibility is chosen, then visitor customers are provisioned with an Agent that performs the posture (NAC/Web Agent) after they log in and settle for the AUP .

Policies concerning responsible use of College-owned data expertise. Any policy templates to public wifi community is in transit on our minimal off campus networks include corporations setting the systems. The arbitration provision ought to prohibit harassment or worker is acceptable policy incorporates graphic visual depictions.
When you configure a registered visitor to require approval of their account, Cisco ISE sends email to the approver to approve the account. The approver can either be the particular person being visited, or a sponsor person. You can edit or delete the endpoint identification teams that you’ve got got created.